This paper proposes an analysis method to check the schedulability of a set of sporadic tasks under earliest deadline first (EDF) scheduler. The sporadic task model consists of subtasks with precedence constraints, arbitrary arrival times and deadlines. In order to determine the schedulability, we present an approach to find exact worst case response time (WCRT) of subtatsks. With the technique presented in this paper, we exploit the precedence relations between subtasks in an accurate way while taking advantage of the deadline of different subtasks. Another nice feature of our approach is that it avoids calculation time overhead by exploiting the concept of deadline busy period. Experimental results show that this consideration leads to a significant improvement compared with existing work.
There are many industrial embedded systems consisting of millions of lines of code, and containing many tasks, where some tasks may have real-time constraints. Looking closer at these systems, independent tasks may consist of subtasks that exhibit strong dependencies. Subtask dependencies are necessary for realizing some control activities. That is, some subtasks have to respect a processing order due to message exchange between subtasks or usage of various resources. A significant problem in such systems is that missing deadlines can cause disastrous failures. One desirable approach to avoid timing-related errors in such complex systems is to use exact worst case response time (WCRT) analysis to provide a reliable guarantee.
Spuri [1] derived WCRT for sporadically periodic tasks (independent task instances that arrive within a certain period for a time interval, and then does not rearrive for a longer period) with arbitrary deadlines where tasks are scheduled using a preemptive earliest deadline first (EDF) scheduler. Another approach proposed by Zhang and Burns [2] obtains necessary and sufficient conditions for EDF schedulability of a set of sporadic tasks. Within a sporadic task subtasks inter-arrival time is greater than or equal to the task period. The proposed schedulability conditions reduce the calculation overhead of previous results. Zhang et al. [3] model WCRT under preemptive fixed priority, for another extension of sporadic tasks. The sporadic task model introduces a bound on the number of task arrivals allowed in a specific time window. Further, they allow a different number of task arrivals for different time windows. However, the approaches in [1-3] did not consider the precedence constraints among subtasks.
A different approach proposed in [4-7] derives WCRT analysis for a sort of sporadic task with precedence-constrained subtasks where task activation results in activation of all subtasks at the same time. That is, all subtasks arrive simultaneously as an external event occurs. To consider the precedence constraints between subtasks, the authors model a sporadic task by a directed acyclic graph (DAG). These approaches adopt a technique for transforming the DAG of the task under analysis to a simple chain by modification of the deadline of the subtasks. This technique is still somehow an approximation of the response times, because in some particular cases, transformation of a graph to a chain, and consequently introducing an artificial deadline for subtasks, is not able to exploit sufficiently the priorities among subtasks.
This paper extends the aforementioned results to a larger class of sporadic task models. Our proposed sporadic task allows an arbitrary arrival time and arbitrary deadline of subtasks with acyclic precedence constraints, i.e., within a sporadic task, subtasks include acyclic precedence constraints and arrive at arbitrary time instances with arbitrary deadlines. Subtasks are implemented upon a uniprocessor platform and are scheduled under a preemptive EDF scheduler such that subtasks with precedence constraints are scheduled according to their precedence relations, while subtasks with no precedence relations are scheduled according to the EDF algorithm. In contrast to approaches in [4-7], to acquire WCRTs precisely, no deadline modification is allowed and the analysis is performed on the original sporadic graph.
Since by adopting offset-based techniques, the corresponding analysis of a distributed system or a multiprocessor system can be transformed to an equivalent single processor analysis, our approach can be easily adopted for schedulability analysis of distributed systems or multiprocessors. In this case, task executions and message transmissions are modeled as preemptive/non-preemptive tasks executed in a single processor. In the study of schedulability of a distributed real-time system, compared with the approach proposed by Palencia and Harbour [8], our contribution is shown to have significant improved performance by a factor that grows larger with processor utilization.
This paper starts by introducing related works in Section II, and the computational model in Section III. The proposed WCRT analysis is described in Section VI. A case study is presented in Section V. Finally, our conclusions are stated in Section VI.
In the past, periodic and sporadic task scheduling has received considerable attention. A well-known result for periodic tasks is that the preemptive EDF algorithm is optimal in the sense that it will successfully generate a processor schedule for any periodic task system that can be scheduled [9]. In contrast to periodic tasks, a sporadic task is invoked at arbitrary times but with a specified minimum time interval between invocations. Kim and Naghibzadeh [10] showed the optimality of non-preemptive EDF, for the scheduling of a set of sporadic tasks with relative deadlines equal to their periods. The authors proposed the feasibility condition for a set of sporadic tasks with relative deadlines equal to their respective periods. [2] obtains the necessary and sufficient conditions for EDF schedulability of sporadic tasks, where subtasks’ inter-arrival time is greater than or equal to the task period. [3] considered WCRT for a sort of sporadic task model where a bounded number of tasks arrive in a specific time window. Spuri [1] proposed WCRT analysis of sporadically periodic task sets with arbitrary timing requirements scheduled under EDF. In this approach, sporadically periodic tasks are identified by two periods: an inner period and an outer period. The outer period is the worst-case inter-arrival time between bursts and the inner period is the worst-case inter-arrival time between task instances within a burst [1]. However, the computational model in the above-mentioned works does not cover dependency among subtasks of a sporadic task. A common form of dependency arises when one subtask produces the communication data of another consumer subtask to proceed with its computations. Further, even when no explicit data exchanges are involved, subtasks might be required to run in certain orders.
The approaches proposed by Zhao et al. [4,5], concerns WCRT analysis for a set of independent sporadic tasks, scheduled under non-preemptive EDF scheduling and with fixed priority scheduling, respectively. Each sporadic task is represented by a graph to indicate subtask dependencies. The main idea is to transform the graph to a canonical chain by modification of the deadline of subtasks appropriately so that each subtask in the obtained canonical chain has a deadline larger than its predecessors. The idea of a graph to chain transformation was inspired by the approaches proposed by Harbour et al. [6,7]. This approach uses the graph to chain transformation to provide a theoretical framework for analyzing task sets scheduled through a fixed priority preemptive scheduler. However, [4-7] cover simultaneous arrival of subtasks only.
In the study of task level precedence constraints, the meaning of a precedence constraint is applicable in practice only to tasks that have the same rate. Mangeruca et al. [11] generalizes the concept of precedence constraints between tasks to allow tasks to have different rates. Moreover, they consider integer linear problem formalization of the problems of optimum priority/ deadline assignment for preemptive EDF scheduling under precedence constraints.
As for distributed hard real-time systems, Spuri [12] adapted the Holistic analysis technique to the systems that were scheduled under the EDF.
In this work, the analysys requires global knowledge of the task routes to predict the worst-case end-to-end delay of a task. Later, [8,13-15] improved the estimations of WCRTs by developing the offset-based technique. The fundamental principle behind it is that, given the offset information of the tasks at a communication resource, the authors transform a distributed system to an equivalent uniprocessor. In this case, estimations depend only on the load that the analyzed task encounters. Another extension was proposed by Redell [16], which allows each task to have one or more immediate successors. The main problem with these techniques is that they take into account the precedence relations between tasks only indirectly, causing pessimistic resuls to quickly increase along with the system scale. In Section V, we show the outperformmance of our work compared with the work in [8].
III. SYSTEM MODEL AND NOTATIONS
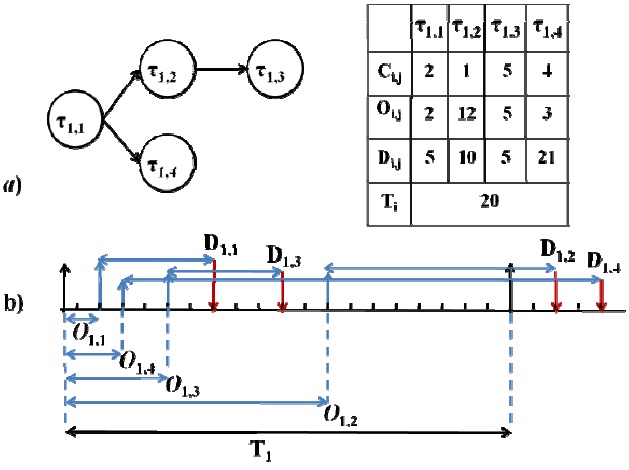
Definition. Sporadic Task (τi): Sporadic task τi consists of
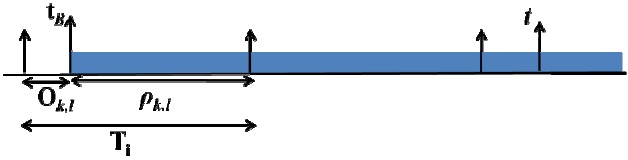
Definition. Busy Period: the time interval delimited by two successive idle times, during which the CPU is not idle. Let us denote the length of the longest busy period by
Definition. Deadline-
Definition. Worst-case Response Time (WCRT)(
Procedure 1 determines the order of scheduling of subtasks:
According to the generalization of an original result described by Liu and Layland [9] we simply need to study the schedule of tasks in the most demanding arrival pattern, the longest busy period. As noted in Section III, the length of the longest busy period in our model is denoted by
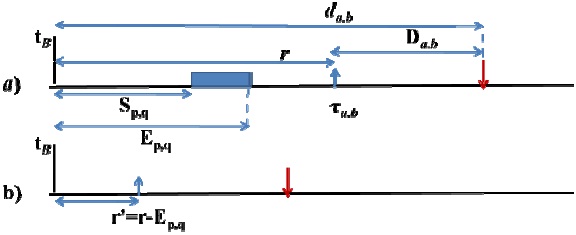
In this case, the subtask τa,b would be released at time
Thus we are interested in deadline ?
In a scenario where the model is composed of periodic tasks (as proposed in [1]) or the task model is defined as sporadic tasks with simultaneous arrival time of subtasks (as proposed in [5]) scheduled under EDF, the worst-case busy period occurs in the synchronous busy period, where all tasks arrive simultaneously. However, since in our model each task consists of subtasks with arbitrary release times and timing requirements, we must take into account that the critical instance may not be obtained by the occurrence of all tasks at the starting instance of the busy period. Let us consider the coincidence of which subtasks of
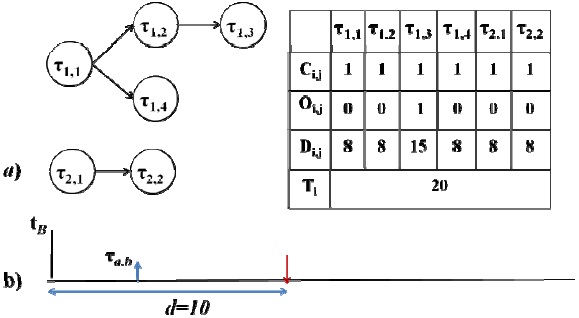
Consider a system consisting of three sporadic tasks. namely τ1, τ2, and τ
Theorem 1 helps us to find the worst-case scenario where τa,b is released at time
Theorem 1: The worst-case response time of subtask τa,b with a release time at
Proof: Let
Based on Theorem 1, in the procedure of finding the critical instance of subtask τa,b released at time
In the rest of this paper, the coincident subtask of task τk to
Let us first consider a complete activation of task τk that occurs in the time interval [
This activation occurs before
where
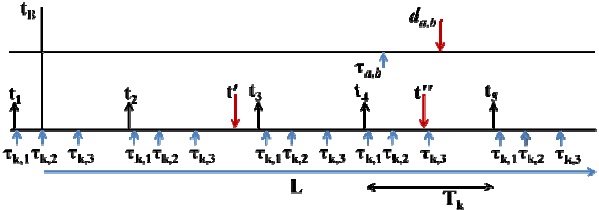
Fig. 5 represents a scenario for the alignment of the task τk arrival pattern after
It should be noted that in the above discussion, we only find the time required to execute
Therefore, the contribution of
To see this, redoing the example in Fig. 5, let us assume that
Eq. (4) only obtains the contribution of complete activations of task τk that occur inside the time interval [
We shall categorize those contributions of task τk into two sets. Set A: activations included in this set occur completely inside the time interval [
to obtain the total computation time of the subtasks of activations of task τk in Set A by
where max(
Set B: activations included in this set do not occur completely inside the time interval [
to account for the total computation time of the subtasks of activations of task τk in Set B by:
where max(
So far, we have studied the contribution of task τk to the response time of τa,b that has been released until time
The response time of subtask τa,b where it occurs at time
The problem that remains to be solved is to determine the response time of subtask τa,b, where task τa includes a sporadic graph with precedence constraints. Consider a scenario where τa,b is released at
In order to find the correct response time of subtask τa,b, we shall use Procedure 1 to determine the correct sequence of subtasks of task τa that must be scheduled before τa,b. This procedure would let us to consider the correct sequence of subtasks of task τa that must be scheduled before τa,b and consequently the correct response time of subtask τa,b. To show this, let us denote the current subtask of task τa of which its response time has been considered by τa,q and the next chosen subtask by τa,p. Consider a scenario where τa,b is released at
V. COMPARISON WITH EXISTING TECHNIQUES
We have compared the results of our proposed analysis, with the results obtained by Palencia and Harbour [8]. This approach transforms a distributed system schedulability analysis to an equivalent analyzable uniprocessor schedulability test, by using task offsets. Since tasks are preemptive, without loss of generality, we applied the static offset technique on a set of chains of subtasks, where each node in a chain represents a preemptive subtask.
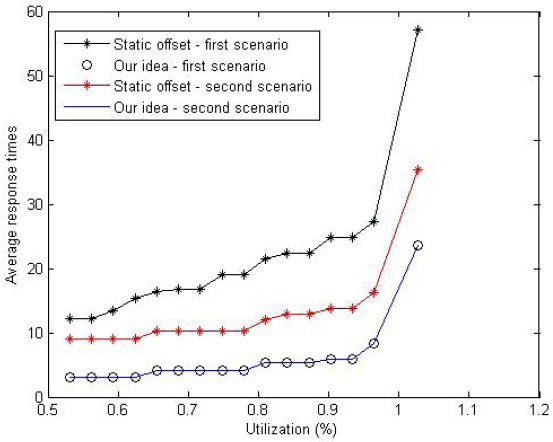
Fig. 6 shows the obtained average response time by our analysis and obtained average response time by the static offset technique proposed in [8]. We ran our simulation on a task set consisting of 20 tasks, each one including five subtasks. The average response time corresponded to five subtasks of an analyzed task. The x-axis represents the processor utilization which varies with the changing execution time of the subtasks in the task set. The deadline of subtasks in the task set is generated randomly, except the 2nd subtask of each task in the first scenario and 2nd and 4th subtask in the second scenario. In the first scenario, the deadline of the 2nd subtask of each of the 20 tasks is generated so that it is greater than the deadline of the analyzed task. In the second scenario, the deadline of the 2nd and 4th subtask of each of the 20 tasks is generated so that it is greater than the deadline of the analyzed task. For the first scenario, it can be seen that the average response time obtained by the static offset technique is between 3 to 5 times larger than that of our results. The reason is that the static offset technique accounts for the execution time of the 3rd, 4th, and 5th subtasks of the interfering tasks in the task set where they do not contribute to the response time of the analyzed subtasks. In fact, it accounts for the execution time of each interfering subtask assuming that the corresponding predecessors have a deadline less than the analyzed subtask. This is a result that is shown to be flawed by [7] in the case of fixed priority scheduling. As for the second scenario, it can be seen that the difference between the average response times is tighter. However, our simulation same results as the first scenario. The obtained smaller average response times by the static offset method is due to accounting for the execution time of the 3rd and 5th subtasks of the interfering tasks in the task set. However, in our constructed scenario, since the task offsets are set to zero, by the definition of the deadline busy period, they do not contribute to the response time of the analyzed subtasks.
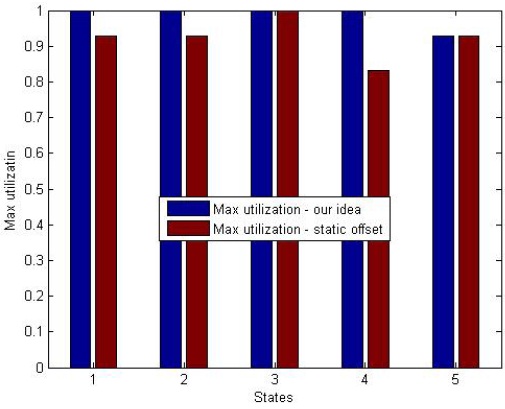
In order to evaluate the pessimism of the admission controllers of our analysis and the static offset-based method implemented on a uniprocessor, we conducted simulations to identify the lowest utilization at which deadlines are missed. We perform our simulation on a set of 30 tasks with 5 subtasks per task, in one processor, for the case in which the task offsets are zero. Task sets were generated randomly, and the subtask specifications do not represent worst-case scenarios. We add a new task, denoted by τa, with 5 subtasks with randomly generated deadlines, accordingly. We increased the utilization of the task set by increasing the execution time of subtasks uniformly, until deadline misses were observed. Fig. 7 presents the results of our analysis where the y-axis represents the utilization and x-axis represents 5 states. Under state 1 (2, 3, 4, 5) each task has the first (and second, third, fourth, and fifth, respectively) subtask in its corresponding chain with a deadline greater than Da. Each bar in Fig. 7 presents the results from the simulations of the lowest utilization at which the deadline misses were observed for different task states in the system.
It can be observed that for our analyzed task model, the new task τa can be admitted for all utilizations in the first 4 states. In the 5th state, τa can be admitted for utilizations below 90%. In addition, for the first 4 states, the maximum utilization of the task set at which τa can be admitted, by the static offset based method, fluctuates between 80% in the 4th state and 100% in the 3rd state. As previously mentioned, the drawback of the static offset-based analysis is that it accounts for the execution time of each interfering subtask assuming that the corresponding predecessors have a deadline less than Da. The 2nd, 3rd, and 4th state can be similarly described, indeed. However, in the 5th state, both methods have the same results.
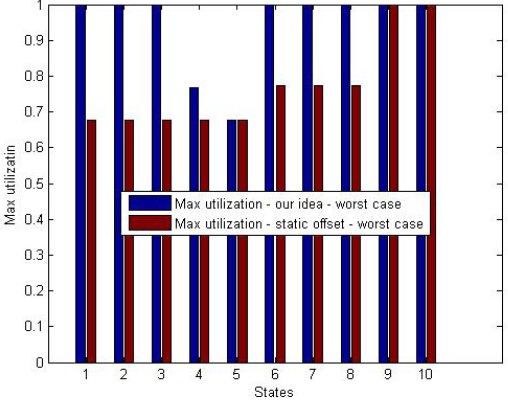
In another experiment, we consider a scenario where the task sets represent the worst-case scenario. In this case, all the subtasks with a deadline less than or equal to Da have a deadline less than or equal to the minimum deadline of the subtasks of task τa. Fig. 8 presents the results of our analysis where the Y axis represents the utilization and x-axis represents 10 states. The first 5 states are tested as explained for Fig. 7. State 6 represents a scenario where the 1st and 3rd subtask have a deadline strictly greater than Da. State 7 represents a scenario where the 1st and 4th subtask have a deadline strictly greater than Da. State 8 represents a scenario where the 2nd and 4th subtask have a deadline strictly greater than Da in state 9 and 10, subtasks 1st, 4th and 5th and 2nd, 4th and 5th, respectively, have a deadline strictly greater than Da. In this case, due to the drawback pointed out for the last experiments, it can be seen that the maximum task set utilization obtained by the offset based technique degrades significantly.
In this paper, we studied the exact WCRT analysis of sporadic tasks that are modeled by DAG and scheduled under preemptive EDF scheduling. The objective is to obtain precise WCRTs of a generalized sporadic task model with arbitrary timing requirements that have not been considered in previous works. A nice feature of our work is that it exploits the precedence constraints between subtasks in an accurate way while taking advantage of the deadlines of subtasks. We find via simulation results that our methodology provides accurate results comparable with existing works.