In recent years, significant developments in wireless and electronic communications have enabled the expanded use of limited-power and small size sensor nodes. A large number of these sensor nodes are deployed in the geographic area and are utilized in a wide range of applications including monitoring physical and artificial environmental phenomena, events, and vehicle tracking [1]. This kind of network is called a wireless sensor network (WSN).
In a WSN, a sensor node consists of three basic units: sensing, processing and communication. The job of the sensing unit is to sense different occurrences around its location and pass the sensed data to the processing unit. The processing unit can process and packetize the sensed data, and the transmission unit can send the packetized data to a base station (sink node) via multi-hop routing [2]. In a WSN, the transmission and sensing range are associated with a sensor node. In a WSN, a sensor node is capable of detecting every event happening within a circular area around itself called its sensing range. Similarly, a sensor node is capable of communicating with all other sensor nodes located within the circular region called the transmission range.
To increase the network lifetime, several techniques, including sleep scheduling and density control, have been used to reduce the energy consumption in a sensor network. The lifetime of wireless sensor networks are greatly affected by the limited transmission range and the restricted battery power of sensor nodes. The lifetime of a WSN is typically determined by the battery power of the critical sensor nodes. Therefore, strategies are required to efficiently use such critical nodes to extend and guarantee the lifetime of the WSN as a whole.
Real-time applications in wireless sensor networks require efficient utilization of the network resources and effective access to sensor data. Therefore, both energy and quality of service (QoS) awareness are involved in different layers of the protocol stack of a real-time application. In real-time applications, the main challenge is to guarantee that the data packet meets its deadline in the network. In such applications, such as a natural disaster monitoring system, the energy consumption is of secondary importance. To support real-time application in a WSN, a real-time communication protocol must adjust its routing performance based on packet deadlines.
In this paper, we propose a real-time communications protocol for a sufficient number of sensor nodes deployed randomly in the target field of a WSN. In our proposed method, we make use of two protocols in different environments: satisfied or unsatisfied cases. Under normal conditions, an existing protocol such as SPEED is employed for data communications. This protocol works continuously until the real-time service is satisfied. On the other hand, when the real-time service is not available, the proposed scheme starts operation by establishing a different path containing of a node that conserves energy much more than an ordinary node. This node is called the agent node for real-time communications. The real-time communication via agent node is conducted by adjusting the transmission range of the sending node. By the agent node hop count from the source to the sink is reduced. Thus, the end-to-end delay is also shortened because the delay is very sensitive and related to the number of intermediate hops.
The rest of this paper is organized as follows. In section II, we review and discuss the previous work done in related areas. In section III, we present our proposed algorithm for real-time applications in detail. In section IV, we discuss and analyze our simulation results. Finally, we provide conclusions and a critical summary in section V.
A great deal of research work has been performed for managing the battery on a sensor node. The results have been to mainly extend the operating lifetime of wireless sensor networks. In [4], It says below that they guaranteed coverage and connectivity. They proposed instruction-level parallelism (ILP) for determining the minimum number of relay nodes as a cluster head and considered the two-tiered network architecture. In their work, they focused on guaranteed connectivity and coverage but did not calculate the guaranteed lifetime. Centralized algorithms can provide more accurate results than distributed algorithms in terms of sensor nodes scheduling.
[1, 5, 6] used a centralized approach for scheduling and prolonging wireless sensor network lifetime. In [6], the authors used coverage and connectivity parameters to decide the scheduling of sensor nodes. When the algorithm is executed the network is reconfigured and the energy consumption is balanced among the sensor nodes. In dynamic sleep scheduling protocol (DSSP), the authors designed a scheme for increasing the lifetime of a dense sensor network by defining a scheduling algorithm. The paper contributes an increased lifetime and coverage of a sensor network but no other QoS parameter or guaranteed lifetime is discussed.
In [7], the authors proposed a scheduling scheme to increase network lifetime and decrease network overall energy consumption by turning off some redundant nodes. A distributed approach is used to schedule nodes between sleep and active mode. Two different schemes were used to solve the coverage problem of the sensor network. The protocol offers good coverage and an extension of lifetime but no guarantee for real-time or other QoS parameters.
In [3], the authors proposed a distributed adaptive sleep scheduling algorithm (DASSA) or a wireless sensor network with partial coverage. DASSA used a centralized approach to maximize the network lifetime subject to connectivity and partial coverage constraints, without requiring the location information of the sensor nodes. The residual energy of the nodes and feedback from the sink node is used to periodically wake up the sensor nodes and determine their scheduling activity for the next round. The WSN is divided into square grids and network operations are divided into rounds.
SPEED [8] and MMSPEED [9] are QoS based routing protocols that provide soft end-to-end deadline guarantees for real-time packets in sensor networks. Both use a geographic forwarding mechanism to route packets to the sink. SPEED ensures a network wide speed of packet delivery for a real-time guarantee, i.e., it calculates the end-to-end delay by dividing the distance to the sink by the speed of packet delivery before making any admission decision. SPEED can also provide congestion avoidance when the network is congested. MMSPEED is an extension of SPEED; MMSPEED generalized the single network wide speed approach of SPEED by replicating and using multiple SPEED layers that run independently from each other. For delivery timeliness, MMSPEED provides multiple network wide packet delivery speed options for different traffic types according to their end-to-end deadlines. For QoS reliability, multipath forwarding is used to control the number of delivery paths based on the probability of reaching end-to-end. However, neither SPEED nor MMSPEED considered the energy consumption metric or the lifetime of the WSN.
In this section, we explain the proposed scheme consequently. These phases include agent node discovery, the real-time protocol for normal conditions, and the real-time protocol for unsatisfied conditions. The main contribution of this paper is especially focused on the last one of these three.
>
A. Agent Node Discovery and Path Establishment
An agent node is defined as the special node that works for real-time communications. Unlike the ordinal node, this node keeps its energy by avoiding normal sensor activities such as sensing and communications. That is, if a node is designated as an agent, the mission of this node is limited to real-time communications instead of other actions.
To find and designate an agent node, a sink node broadcasts an AGENT_REQUEST message into the whole network. When each node identifies itself as a leaf node by checking its geographic position, it replies with an AGENT_REPLY message while adjusting its transmission range maximally. To identify the agent node, the following steps are taken.
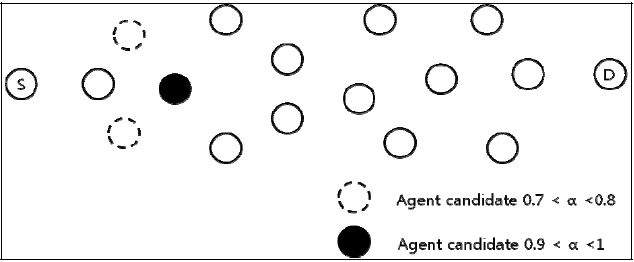
Step 1: Each source node broadcasts an AGENT_REPLY message including the position information of the sending node, and the expected distance by a general equation. If each node receives this message, it measure the distance from the source to itself. If the distance between the two nodes ranges from a predetermined threshold to the maximum, the node is regarded as a candidate node. In Fig. 1, the dashed nodes are within the boundary from 0.7 × maximum distance to 0.8 × maximum distance. Also, black colored node is within from 0.9 to 1. The reason that the two types of nodes are chosen is that we will establish multiple paths according to the requirements.
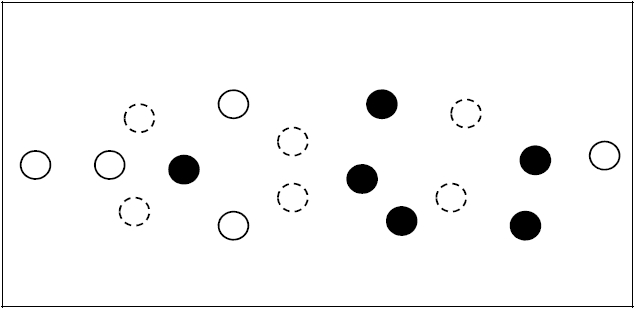
Step 2: After receiving an AGENT_REPLY message, a candidate node rebroadcasts the AGENT_REPLY message toward the sink node until the sink node receives it. Each node inserts its address into the AGENT_REPLY message to indentify the backward node. In Fig. 2, we can see the example for a situation in which the agent discovery phase is completed.
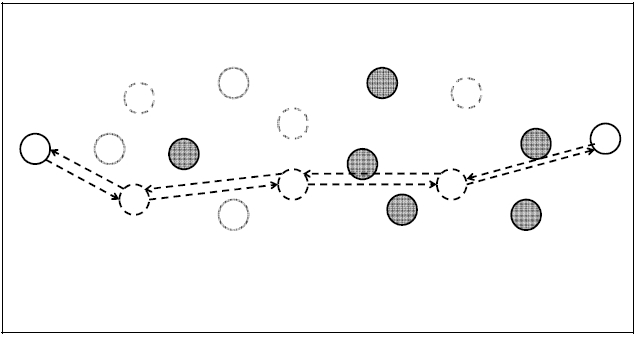
Step 3: After the sink node receives the AGENT_REPLY node carrying the intermediate node information, it builds a topology that consists of multiple candidate nodes. The path establishment algorithm is then conducted. For the primary path, the shortest path algorithm is employed. This is because the shortest path can contribute to reducing delay by reducing the number of hops. In Fig. 3, one path is established as a primary path between the source and sink. The path setup is accomplished by AGENT_ACK and AGENT_CONFIRM messages.
Step 4: For the secondary path, a disjoint secondary path setup is required. To achieve this, intermediate nodes along the primary path are excluded when it comes to computing the secondary path. For the secondary path, the shortest path algorithm is also employed and the same message is used to establish the path. Fig. 4 demonstrates the phase for secondary path establishment.
Under normal conditions, for simplicity, the well-known SPEED protocol is used to guarantee real-time communications. However, whenever the requirement for real-time is not met, the primary and secondary paths are used to deliver real-time packets. To activate the secondary path, a source node notifies the source that the real-time service is not being met by SPEED.
After receiving the path from the source, the source node adjusts its transmission power to reach the nearest node along the secondary path. And then, it sends the next real-time packets to it. When the next node receives a packet, it sends it to the following node along the path, which comprises the secondary path.
Depending on the quality of the secondary path, there are three choices for real-time communications: 1) return to the normal protocol (SPEED), 2) maintain the current secondary path, 3) use the primary path. For case 1) and 2), we need to measure the current quality of the real-time service. To achieve this, a source establishes two paths sequentially. First, a data packet is transmitted along the secondary path by adjusting the transmission range for one time period. After one time period is over, the source node sends real-time packets along the normal path in SPEED. When the real-time service is available to meet requirements through SPEED, the source node maintains transmission power to the normal node. Otherwise, the source node keeps the transmission power adjusted for delivery of real-time service.
The last case is accomplished when real-time service is not met by transmission along the secondary path. In this case, the source and agent nodes increase their transmission power maximally so it can reach the destination along the minimum number of hops. Similar to previous cases, the path selection algorithm concerns the three cases based on the current traffic load and quality of real-time service. That is, the primary path can be replaced by the secondary path, not the normal path.
>
A. Simulation Model and Environment
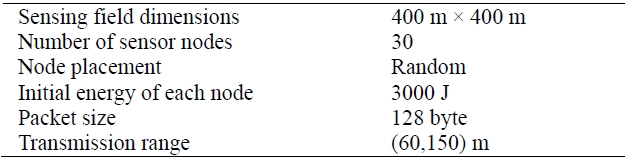
In order to evaluate the performance of our proposed algorithm, we conducted simulations in OPNET 14.5 by considering the parameter values shown in Table 1. We used the ZigBee IEEE 802.15.4 specification model with changes in the network layer and battery module [10].
[Table 1.] Simulation parameters
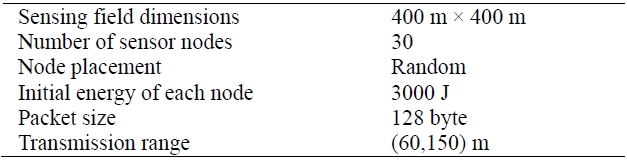
Simulation parameters
General carrier sense multiple access (CSMA) was used for medium access control (MAC) protocols and a two-ray model was executed for the propagation models. The application used for this simulation was SURGE, which reported the sensing information at the constant rate of a predetermined period. Without any mention of simulation scenarios, the mean period of a stream was 50 ms with the period defined as the inter-arrival time between packets in a stream.
Multiple runs with different seed numbers were conducted for each scenario and data collected was averaged over those runs.
>
B. Simulation Results and Analysis
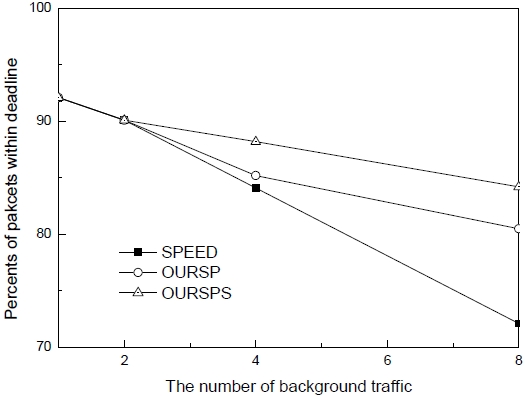
In Fig. 5, we evaluated the performance for how much real-time traffic is delivered within the deadline. We compared the three protocols, that is, the original SPEED, ours with the primary path labeled as OURSP, and ours with the primary and secondary path, labeled OURSPS. Our protocol with the primary path means that there is only one additional real-time path, which consists of nodes with maximum transmission power. The performance was evaluated as the amount of background traffic increases. For all the protocols, fewer packets were delivered to the sink when there were many traffic sources. However, as compared to the original SPEED protocol, our protocol with the primary and secondary path showed the best performance. This is mainly because there is no additional protocol in SPEED when real-time service is not available. In addition, two kinds of additional paths contribute to improved performance. Through the disjoint paths, real-time traffic will be distributed so the end-to-end delay is decreased. However, if the primary path is established, the impact of these are reduced. This produces the difference between the two versions of the proposed scheme.
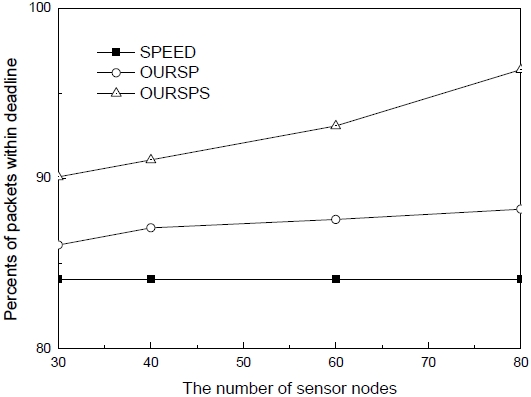
Another simulation was conducted to evaluate the performance of the proposed scheme as a function of the number of sensor nodes. As seen in Fig. 6, the SPEED protocol has no impact on the performance as the number of sensor nodes increases. Since SPEED chooses the next hop without regard to traffic load or other factors except for the velocity, the number of sensor nodes has no effect on the performance. On the other hand, the proposed scheme can improve performance where there are many sensor nodes. Since the agent discovery procedure is repeated periodically, diverse paths are established in the proposed scheme according to the corresponding traffic load. Also, since there is a high probability out of discovering disjoint paths where many sensor nodes are located within the territory. If any node is used again in a different path, the two paths are not always available, so low performance is depicted in Fig. 6.
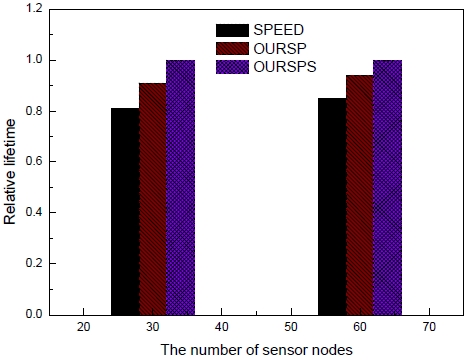
The last simulation result is illustrated in Fig. 7. In this figure, the lifetime of the networks is compared where the three protocols were employed for real-time communi-cations. Each case is represented as a value relative to OURSPS. As seen in Fig. 7, the lifetime of networks employing SPEED is shorter than the lifetime of ours. The main reason for the shortened lifetime is the same as that described for both Figs. 5 and 6. That fact indicates that an extended lifetime can be also achieved by the proposed scheme by avoiding transmission along the one main path for real-time communications.
In order to support real-time service in WSN, some research studies have been proposed. However, due to their high complexity, it is not easy to employ them in a real environment. In this paper, we proposed a new real-time routing protocol by adjusting the transmission power efficiently. The proposed scheme makes use of a different routing scheme depending on the current quality of the real-time service and transmitting path. Finally, performance evaluation through several simulation scenarios was conducted to demonstrate that the proposed scheme is more suitable than a well-known protocol regarding real-time service requirements.
Related to this work, a specific traffic model and strict real-time model will be needed. Also, more studies for performance evaluation will be carried out through various topologies as well as adjustable parameters to determine the strengths and weaknesses of the proposed scheme.